Operation Completes by Is Required Please Specify a Value and Try Again
This document describes how to install a Locally Significant Certificate (LSC) on a Cisco Internet Protocol Telephone (Cisco IP Phone).
Requirements
Cisco recommends that you have noesis of these topics:
- Cisco Unified Communications Managing director (CUCM) Cluster Security Manner options
- X.509 certificates
- Manufacturing Installed Certificates (MICs)
- LSCs
- Document Authority Proxy Function (CAPF) certificate operations
- Security Past Default (SBD)
- Initial Trust List (ITL) files
Components Used
The data in this document is based on CUCM versions that back up SBD, namely CUCM 8.0(one) and above.
Notation: It too merely pertains to phones that support Security Past Default (SBD). For example, the 7940 and 7960 phones practice non support SBD, nor do the 7935, 7936 and 7937 conference phones. For a list of devices that support SBD in your version of CUCM, navigate to Cisco Unified Reporting > System Reports > Unified CM Phone Characteristic Listing and run a report on Feature: Security By Default.
The data in this certificate was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make certain that you understand the potential affect of any control.
MICs versus LSCs
If you use certificate based authentication for 802.1X or Anyconnect Phone VPN, it is important to understand the difference between MICs and LSCs.
Every Cisco phone comes with a MIC pre-installed at the factory. This certificate is signed by one of the Cisco Manufacturing CA certificates, either by the Cisco Manufacturing CA, Cisco Manufacturing CA SHA2, CAP-RTP-001 or CAP-RTP-002 certificate. When the telephone presents this certificate, it proves that it is a valid Cisco phone, simply this does not validate that the telephone belongs to a specific customer or CUCM cluster. It could potentially be a rogue phone purchased on the open up market or brought over from a dissimilar site.
LSCs, on the other hand, are intentionally installed on phones past an ambassador, and are signed by the CUCM Publisher'south CAPF certificate. You would configure 802.1X or Anyconnect VPN to merely trust LSCs issued past known CAPF certificate authorities. Basing certificate hallmark on LSCs instead of MICs provides y'all with a much more than granular control over which phone devices are trusted.
Network Topology
These CUCM lab servers were used for this certificate:
- ao115pub - 10.122.138.102 - CUCM Publisher & TFTP server
- ao115sub - 10.122.138.103 - CUCM Subscriber & TFTP server
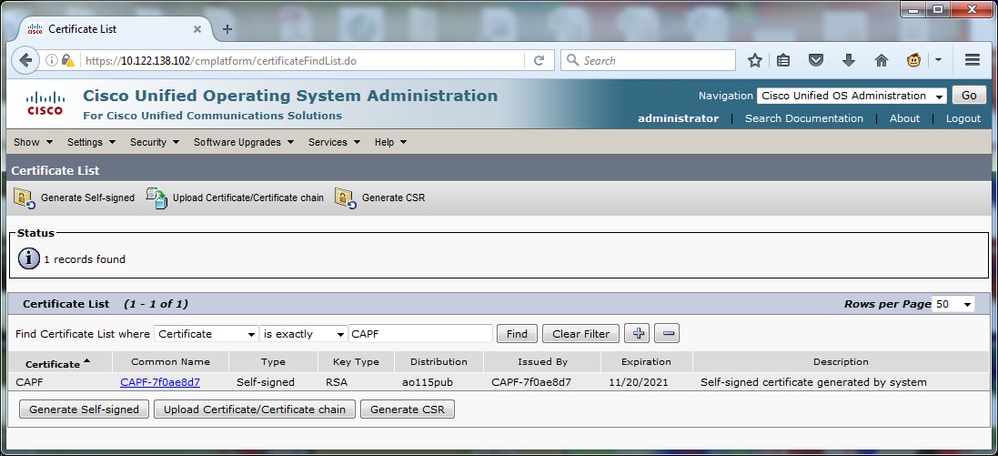
Verify that the CAPF certificate has not expired, nor is about to elapse in the near future. Navigate to Cisco Unified Os Administration > Security > Certificate Management, then Find Certificate List where Certificate is exactly CAPF as shown in the prototype.
Click Common Proper noun in order to open the Certificate Details page. Inspect the Validity From: and To: dates in the Certificate File Data pane in order to determine when the certificate expires, as shown in the image.
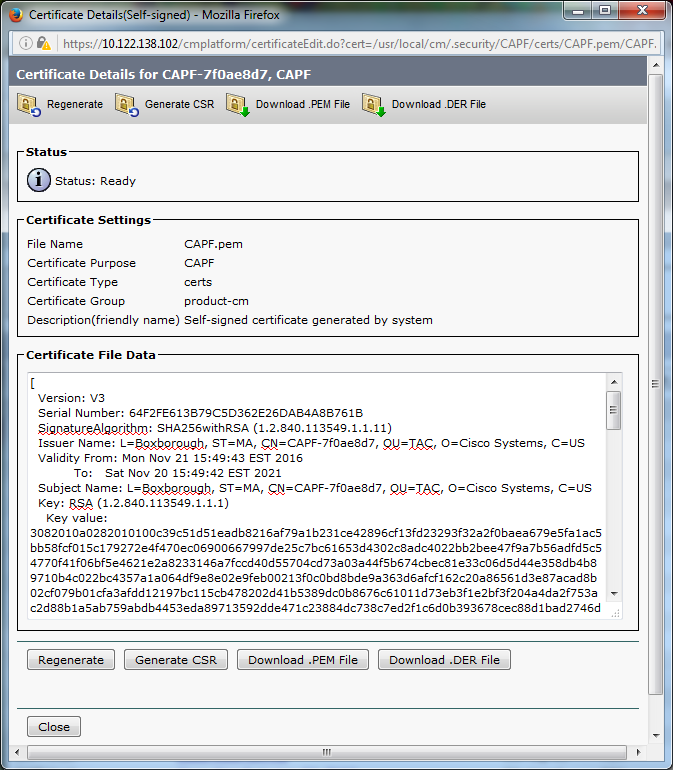
If the CAPF certificate has expired, or is soon to elapse, regenerate that document. Do not motility forward with the LSC install process with an expired or soon to expire CAPF certificate. This avoids the need to reissue LSCs in the near future due to CAPF certificate expiration. For information almost how to regenerate the CAPF certificate, refer the CUCM Certificate Regeneration/Renewal Process article.
Similarly, if you demand to have your CAPF certificate signed by a third party Certificate Potency, y'all take a choice to make at this phase. Either complete the Certificate Signing Request (CSR) file generation and importation of the signed CAPF certificate now, or continue the configuration with a self-signed LSC for a preliminary examination. If you need a third party signed CAPF certificate, it is mostly sensible to configure this feature kickoff with a self-signed CAPF certificate, test and verify, and then redeploy LSCs that are signed past a third party signed CAPF document. This simplifies later troubleshooting, if tests with the 3rd party signed CAPF certificate fail.
Alert: If you regenerate the CAPF document or import a 3rd-party signed CAPF certificate while the CAPF service is activated and started, phones are automatically reset by CUCM. Complete these procedures in a maintenance window when it is acceptable for phones to be reset. For reference, run into CSCue55353 - Add warning when regenerating TVS/CCM/CAPF document that phones reset.
Notation: If your CUCM version supports SBD, this LSC install procedure applies regardless if your CUCM cluster is gear up to mixed mode or not. SBD is a part of CUCM version 8.0(1) and afterwards. In these versions of CUCM, the ITL files contains the certificate for the CAPF service on the CUCM Publisher. This allows phones to connect to the CAPF service in order to support certificate operations such as Install/Upgrade and Troubleshoot.
In the previous versions of CUCM, it was necessary to configure the cluster for Mixed Mode in club to support document operations. Every bit this is no longer necessary, this reduces barriers to the employ of LSCs every bit telephone identity certificates for 802.1X authentication or for AnyConnect VPN client authentication.
Run the testify itl control on all TFTP servers in the CUCM cluster. Observe that the ITL file does contains a CAPF certificate.
For case, here is an excerpt of the show itl output from the lab CUCM Subscriber ao115sub.
Note: In that location is an ITL Record entry in this file with a Function of CAPF.
Annotation: If your ITL file doesn't have a CAPF entry, log in to your CUCM publisher and confirm the CAPF service is activated. In lodge to confirm this, navigate to Cisco Unified Serviceability > Tools > Service Activation > CUCM Publisher > Security, so activate the Cisco Certificate Authority Proxy Function Service. If the service was deactivated and you just activated it, navigate to Cisco Unified Serviceability > Tools > Control Center – Feature Services > Server > CM Services, then restart the Cisco TFTP service on all TFTP servers in the CUCM cluster to regenerate the ITL file. Besides, ensure that yous do not hit CSCuj78330.
Note: After yous're done, run the show itl command on all TFTP servers in the CUCM cluster in gild to verify that the current CUCM Publisher CAPF certificate is now included in the file.
ITL Record #:ane
----
BYTEPOS TAG LENGTH VALUE
------- --- ------ -----
1 RECORDLENGTH 2 727
two DNSNAME 2
3 SUBJECTNAME 64 CN=CAPF-7f0ae8d7;OU=TAC;O=Cisco Systems;L=Boxborough;ST=MA;C=US
four FUNCTION 2 CAPF
5 ISSUERNAME 64 CN=CAPF-7f0ae8d7;OU=TAC;O=Cisco Systems;50=Boxborough;ST=MA;C=US
vi SERIALNUMBER 16 64:F2:FE:61:3B:79:C5:D3:62:E2:6D:AB:4A:8B:76:1B
7 PUBLICKEY 270
eight SIGNATURE 256
eleven CERTHASH twenty C3 E6 97 D0 8A E1 0B F2 31 EC ED 20 EC C5 BC 0F 83 BC BC 5E
12 HASH ALGORITHM 1 nullITL Record #:2
----
BYTEPOS TAG LENGTH VALUE
------- --- ------ -----
i RECORDLENGTH 2 717
2 DNSNAME ii
3 SUBJECTNAME 59 CN=ao115pub;OU=TAC;O=Cisco Systems;L=Boxborough;ST=MA;C=US
iv FUNCTION 2 TVS
5 ISSUERNAME 59 CN=ao115pub;OU=TAC;O=Cisco Systems;50=Boxborough;ST=MA;C=US
6 SERIALNUMBER 16 6B:99:31:15:D1:55:5E:75:9C:42:8A:CE:F2:7E:EA:E8
vii PUBLICKEY 270
8 SIGNATURE 256
11 CERTHASH 20 05 9A DE 20 fourteen 55 23 second 08 20 31 4E B5 9C E9 Atomic number 26 BD 2D 55 87
12 HASH ALGORITHM ane zipITL Record #:3
----
BYTEPOS TAG LENGTH VALUE
------- --- ------ -----
1 RECORDLENGTH 2 1680
2 DNSNAME 2
3 SUBJECTNAME 71 CN=ITLRECOVERY_ao115pub;OU=TAC;O=Cisco Systems;L=Boxborough;ST=MA;C=US
iv FUNCTION two System Ambassador Security Token
5 ISSUERNAME 71 CN=ITLRECOVERY_ao115pub;OU=TAC;O=Cisco Systems;L=Boxborough;ST=MA;C=Us
vi SERIALNUMBER sixteen 51:BB:2F:1C:EE:80:02:sixteen:62:69:51:9A:fourteen:F6:03:7E
7 PUBLICKEY 270
8 SIGNATURE 256
ix CERTIFICATE 963 DF 98 C1 DB E0 61 02 1C 10 eighteen D8 BA F7 1B 2C AB 4C F8 C9 D5 (SHA1 Hash HEX)
This etoken was not used to sign the ITL file.ITL Record #:4
----
BYTEPOS TAG LENGTH VALUE
------- --- ------ -----
ane RECORDLENGTH 2 717
2 DNSNAME 2
3 SUBJECTNAME 59 CN=ao115sub;OU=TAC;O=Cisco Systems;L=Boxborough;ST=MA;C=The states
4 FUNCTION 2 TVS
5 ISSUERNAME 59 CN=ao115sub;OU=TAC;O=Cisco Systems;L=Boxborough;ST=MA;C=The states
six SERIALNUMBER 16 65:E5:10:72:E7:F8:77:DA:F1:34:D5:E3:5A:E0:17:41
7 PUBLICKEY 270
8 SIGNATURE 256
11 CERTHASH xx 00 44 54 42 B4 8B 26 24 F3 64 3E 57 8D 0E 5F B0 8B 79 3B BF
12 HASH ALGORITHM 1 nullITL Record #:five
----
BYTEPOS TAG LENGTH VALUE
------- --- ------ -----
ane RECORDLENGTH ii 1652
2 DNSNAME 2
iii SUBJECTNAME 59 CN=ao115sub;OU=TAC;O=Cisco Systems;L=Boxborough;ST=MA;C=US
four Part 2 System Administrator Security Token
five ISSUERNAME 59 CN=ao115sub;OU=TAC;O=Cisco Systems;50=Boxborough;ST=MA;C=US
6 SERIALNUMBER sixteen 48:F7:D2:F3:A2:66:37:F2:DD:DF:C4:7C:E6:B9:CD:44
7 PUBLICKEY 270
8 SIGNATURE 256
nine Certificate 959 xx BD 40 75 51 C0 61 5C fourteen 0D 6C DB 79 E5 9E 5A DF DC 6D 8B (SHA1 Hash HEX)
This etoken was used to sign the ITL file.ITL Record #:6
----
BYTEPOS TAG LENGTH VALUE
------- --- ------ -----
1 RECORDLENGTH 2 1652
2 DNSNAME two
3 SUBJECTNAME 59 CN=ao115sub;OU=TAC;O=Cisco Systems;L=Boxborough;ST=MA;C=US
iv FUNCTION 2 TFTP
5 ISSUERNAME 59 CN=ao115sub;OU=TAC;O=Cisco Systems;L=Boxborough;ST=MA;C=The states
6 SERIALNUMBER 16 48:F7:D2:F3:A2:66:37:F2:DD:DF:C4:7C:E6:B9:CD:44
7 PUBLICKEY 270
8 SIGNATURE 256
9 CERTIFICATE 959 20 BD forty 75 51 C0 61 5C 14 0D 6C DB 79 E5 9E 5A DF DC 6D 8B (SHA1 Hash HEX)ITL Record #:7
----
BYTEPOS TAG LENGTH VALUE
------- --- ------ -----
one RECORDLENGTH 2 1031
ii DNSNAME 9 ao115sub
3 SUBJECTNAME 62 CN=ao115sub-EC;OU=TAC;O=Cisco Systems;L=Boxborough;ST=MA;C=US
4 Function 2 TFTP
5 ISSUERNAME 62 CN=ao115sub-EC;OU=TAC;O=Cisco Systems;L=Boxborough;ST=MA;C=US
6 SERIALNUMBER 16 53:CC:1D:87:BA:6A:28:BD:DA:22:B2:49:56:8B:51:6C
7 PUBLICKEY 97
eight SIGNATURE 103
9 CERTIFICATE 651 E0 CF 8A B3 4F 79 CE 93 03 72 C3 7A 3F CF AE C3 3E DE 64 C5 (SHA1 Hash HEX)The ITL file was verified successfully.
With the CAPF entry confirmed as an entry in the ITL, you can consummate a certificate operation on a telephone. In this example, a 2048 bit RSA document is installed by use of Null String hallmark.
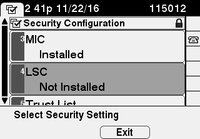
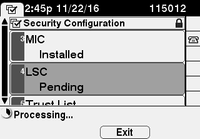
On the phone, verify that an LSC is not yet installed every bit shown in the prototype. For example, on a 79XX series phone, navigate to Settings > four - Security Configuration > 4 - LSC.
Open the phone configuration page for your phone. Navigate toCisco Unified CM Administration > Device > Phone.
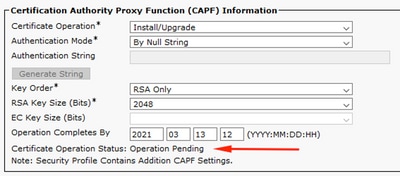
Enter these details to the CAPF Information section of the phone's configuration, as shown in the image:
- For Document Operation, select Install/Upgrade
- For Authentication Mode, select By Null Cord
- For this example, leave the Key Society, RSA Key Size (Bits) and EC Key Size (Bits) set to the system defaults.
- For Operation Completes By, enter a engagement and time that is at to the lowest degree one hour in to the future.
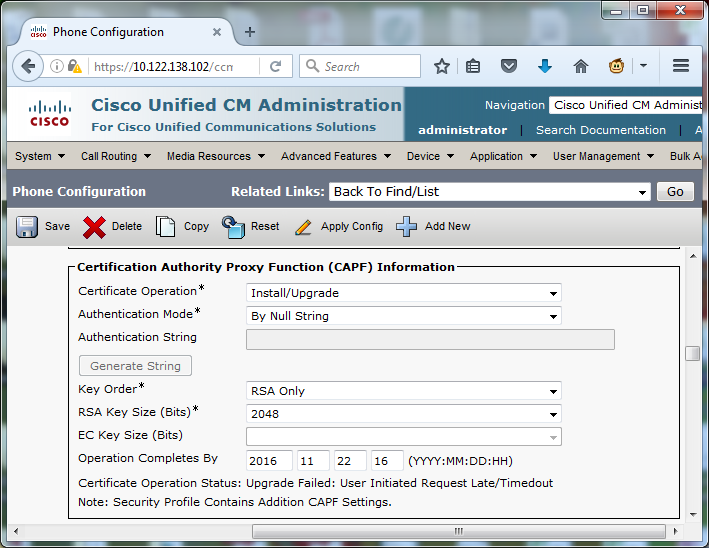
Save your configuration changes, and so Employ Config.
The LSC status on the telephone changes to Pending equally shown in the image.
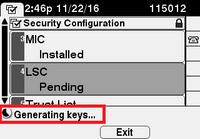
The telephone generates keys as shown in the image.
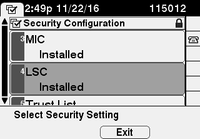
The telephone resets, and when the reset completes, the phone LSC status changes to Installed as shown in the image.
This is likewise visible under Status Messages in the telephone every bit shown in the image.

Utilize this department in order to confirm that your configuration works properly.
In gild to verify LSC certificate installation on multiple phones, refer the Generate CAPF Report section of Security Guide for Cisco Unified Communications Managing director, Release 11.0(ane). Alternatively, y'all may view the aforementioned information within the CUCM Administration web interface by use of the Notice Phones past LSC Condition or Authentication String procedure.
In gild to obtain copies of the LSC certificates installed in phones, refer the How to recall certificates from Cisco IP phonesarticle.
This department provides information y'all tin can utilise in order to troubleshoot your configuration.
No valid CAPF server
The LSC fails to install. The phone's Status Messages bear witness No valid CAPF server. This indicates that there is no CAPF entry in the ITL file. Verify that the CAPF service was activated, then restart the TFTP Service. Verify that the ITL file contains a CAPF certificate afterward the restart, reset the telephone to pick up the latest ITL file, and and so retry your certificate operation. If the CAPF server entry in the phone's security settings carte displays as hostname or fully qualified domain proper noun, ostend the phone is able to resolve the entry to an IP address.
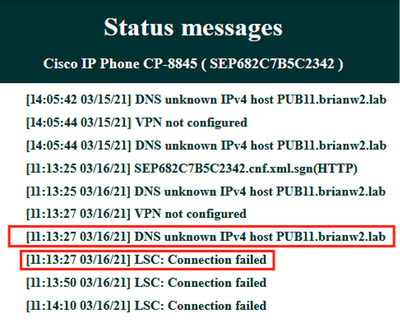
LSC: Connection Failed
The LSC fails to install. The phone's Status Messages prove LSC: Connection Failed. This may signal one of these weather:
- A mismatch between the CAPF certificate in ITL file and the current certificate, the CAPF service is in use.
- The CAPF service is stopped or deactivated.
- The telephone cannot accomplish the CAPF service over the network.
Verify the CAPF service is activated, restart the CAPF service, restart TFTP services clusterwide, reset the phone to pick up the latest ITL file, and then retry your certificate operation. If the problem persists, take a bundle capture from the phone and the CUCM Publisher, and analyze in order to run across if there is bidirectional communication on port 3804, the default CAPF service port. If not, there may be a network issue.
LSC: Failed
The LSC fails to install. The telephone's Status Messages show LSC: Failed. The Phone Configuration web page shows Certificate Operation Status: Upgrade Failed: User Initiated Request Late/Timedout. This indicates that the Functioning Completes By time and date take expired or are in the past. Enter a date and time that is at least 1 hour in to the future, so retry your certificate operation.
LSC: Functioning Pending
The LSC fails to install. The phone's Status Messages show LSC: Connection Failed. The telephone Configuration folio shows Document Performance Status: Operation Awaiting. There are different reasons that one may see the Certificate Performance Status: Operation Pending status. Some of them may include:
- ITL on the phone is unlike than the one currently used on the confugred TFTP servers.
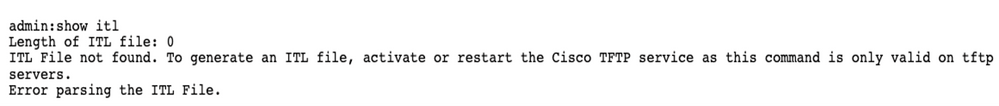
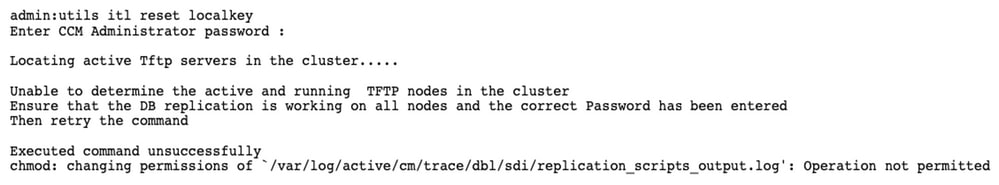
- Issues with corrupt ITL's. When this happens devices lose their trusted status and the command utils itl reset localkey volition need to be ran from the CUCM Publisher to forcefulness the phones to now use the ITLRecovery certificate. If the cluster is in mixed-mode, yous demand to use the command utils ctl reset localkey. Beneath we see an example of what one may meet when attempting to view a corrupt ITL from the CLI of CUCM. If there is the below error when try to view the ITL and attempt to run the utils itl reset localkey command simply encounter the second mistake, this can be a defect CSCus33755. Confirm if the version of the CUCM is affected.
- Phones fail to authenticate the new LSC due to TVS failure.
- Phone use the MIC certificate only the Certificate Authroity Proxy Office (CAPF) Information department on the phones configuration folio has the Hallmark Mode set to "by Existing Document (Precendnce to LSC)".
- Phone is non able to resolve the FQDN of CUCM.
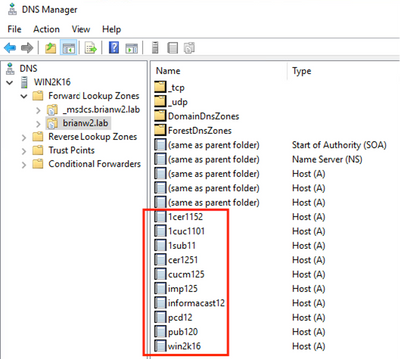
For the last scenario higher up, I've setup a lab surroundings to simulate what nosotros would see in the logs if a phone was not able to resolve the FQDN of CUCM. Currently my lab is setup with the following servers:
- CUCM Publisher and Subscriber running version 11.five.i.15038-2
- Windows 2022 Server setup as my DNS server
For the examination, there is non a DNS entry for the PUB11 CUCM server configured.
Attempted to push an LSC to one of the phones (8845) in the lab. Meet below that it still shows Certiifcate Operation Status: Operation Awaiting.
In the phone console logs, see the phone attempts to query its local chache (127.0.0.i), prior to forrard the query to the configured DNS server accost.
0475 INF Mar 12 fifteen:07:53.686410 dnsmasq[12864]: query[A] PUB11.brianw2.lab from 127.0.0.1 0476 INF Mar 12 15:07:53.686450 dnsmasq[12864]: forwarded PUB11.brianw2.lab to X.X.X.X 0477 INF Mar 12 15:07:53.694909 dnsmasq[12864]: forwarded PUB11.brianw2.lab to X.X.X.Ten 0478 INF Mar 12 15:07:53.695263 dnsmasq[12864]: reply PUB11.brianw2.lab is NXDOMAIN-IPv4 0479 INF Mar 12 15:07:53.695833 dnsmasq[12864]: query[A] PUB11.brianw2.lab from 127.0.0.1 0480 INF Mar 12 15:07:53.695865 dnsmasq[12864]: cached PUB11.brianw2.lab is NXDOMAIN-IPv4 0481 WRN Mar 12 15:07:53.697091 (12905:13036) JAVA-configmgr MQThread|NetUtil.traceIPv4DNSErrors:? - DNS unknown IPv4 host PUB11.brianw2.lab ++ Even so, we encounter that the phone is not able to resolve the FQDN of the CUCM Publisher. This is because nosotros need to configure the DNS entry for PUB11 on our DNS server. 0482 ERR Mar 12 15:07:53.697267 (12905:13036) Java-configmgr MQThread|cip.sec.TvsProperty:? - Failed to resolve Tvs Ipv4 Accost with hostname PUB11.brianw2.lab ++ Afterwards, nosotros run into the CAPF operation neglect. This is expected because we do not have a DNS mapping for PUB11. 0632 Not Mar 12 15:07:55.760715 (12905:13036) Java-configmgr MQThread|cip.sec.CertificateProperty:? - CertificateProperty.setCertificate() authMode=CAPF_AUTH_MODE_NULL_STR authorizationString=goose egg theReason=CAPF_REASON_AUTO 0633 NOT Mar 12 15:07:55.761649 (322:17812) SECUREAPP-RCAPF_START_MODE: First CAPF - mode:[1]([NULL_STR]), reason:[1]([AUTO]) no auth-str 0634 Not Mar 12 15:07:55.761749 (322:17812) SECUREAPP-CAPF_CLNT_INIT:CAPF clnt initialized 0635 Not Mar 12 fifteen:07:55.761808 (322:17812) SECUREAPP-CAPFClnt: SetDelayTimer - set with value <0> 0636 ERR Mar 12 15:07:55.761903 (322:17812) SECUREAPP-Sec create BIO - invalid parameter. 0637 ERR Mar 12 fifteen:07:55.761984 (322:17812) SECUREAPP-SEC_CAPF_BIO_F: CAPF create bio failed 0638 ERR Mar 12 xv:07:55.762040 (322:17812) SECUREAPP-SEC_CAPF_OP_F: CAPF operation failed, ret -7 0639 CRT Mar 12 fifteen:07:55.863826 (12905:13036) JAVA-configmgr MQThread|cip.sec.CertificateProperty$1:? - LSC: Connectedness failed ++ What nosotros would look to run across is something like to the following where DNS replies with the IP address that is associated with the FQDN of CUCM. Afterwards configuring a AAAA record in DNS for PUB11, we at present run across the below consequence in the console logs. 4288 INF Mar 12 xvi:34:06.162666 dnsmasq[12864]: query[A] PUB11.brianw2.lab from 127.0.0.1 4289 INF Mar 12 sixteen:34:06.162826 dnsmasq[12864]: forwarded PUB11.brianw2.lab to 10.10.X.X 4290 INF Mar 12 16:34:06.164908 dnsmasq[12864]: answer PUB11.brianw2.lab is 10.X.X.X 4291 NOT Mar 12 sixteen:34:06.165024 (12905:13036) JAVA-configmgr MQThread|cip.sec.TvsProperty:? - Resolve Tvs Ipv4 Address to Ten.X.X.X from hostname PUB11.brianw2.lab Encounter in the phone status letters below, that the phone is not able to resolve PUB11.brianw2.lab. Afterwards meet the LSC: Connection failed message.
Defects to Consider:
CSCub62243 - LSC install fails intermittently and thereafter information technology freezes the CAPF Srvr
Enhancement Defect to Consider:
CSCuz18034 - Demand reporting for LSC installed endpoints along with expiry status
These documents provide more information on the utilise of LSCs in the context for AnyConnect VPN client authentication and 802.1X authentication.
- AnyConnect VPN Phone - IP Phones, ASA, and CUCM Troubleshooting
- Identity-Based Networking Services: IP Telephony In IEEE 802.1X-Enabled Networks Deployment and Configuration Guide
There is also an advanced type of LSC configuration, in which the LSC certificates are signed directly by a third party Certificate Authority, non the CAPF certificate.
For details, refer: CUCM Third-Party CA-Signed LSCs Generation and Import Configuration Example
- Technical Support & Documentation - Cisco Systems
Source: https://www.cisco.com/c/en/us/support/docs/content-networking/certificates/213295-how-to-install-an-lsc-on-a-cisco-ip-phon.html
0 Response to "Operation Completes by Is Required Please Specify a Value and Try Again"
Post a Comment